Unlock the Secrets of Randomness: A Comprehensive Guide to "Deterministic Extraction from Weak Random Sources"

In the realm of cryptography and information theory, randomness plays a pivotal role. From secure communication to data compression and privacy protection, the ability to generate and manipulate random numbers is of paramount importance. However, practical applications often face the challenge of obtaining sufficiently high-quality randomness.
"Deterministic Extraction from Weak Random Sources: Theory and Applications" offers a definitive guide to understanding and leveraging this crucial technique. Authored by leading experts in the field, this comprehensive monograph provides an in-depth exploration of the theory, algorithms, and practical applications of extracting deterministic randomness from weak random sources.
4.9 out of 5
| Language | : | English |
| File size | : | 9285 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 306 pages |
Key Concepts and Definitions
The concept of "weak random sources" refers to sources that produce sequences of symbols or bits with limited randomness. These sources may exhibit biases, correlations, or other non-ideal characteristics.
"Deterministic extraction" is a technique that aims to extract a deterministic and unpredictable sequence of bits from such weak random sources. This process involves applying carefully designed algorithms that amplify the randomness present in the source, effectively transforming it into a stronger source of randomness.
Core Principles and Algorithms
The foundation of deterministic extraction lies in the principles of information theory and probability. The authors present a thorough analysis of the theoretical underpinnings of the technique, explaining concepts such as entropy, min-entropy, and statistical distance measures.
They delve into the core algorithms used for deterministic extraction, including the Leftover Hash Lemma, the Wegman-Carter algorithm, and universal hashing. The detailed explanations and formal proofs provide a deep understanding of how these algorithms operate and their limitations.
Applications in Cryptography and Beyond
The practical applications of deterministic extraction are wide-ranging and have a significant impact on various fields. The authors explore the use of deterministic extraction in:
* Cryptography: Generating cryptographic keys, randomness beacons, and online gambling protocols * Data Compression: Lossless data compression using Universal Lossless Data Compression (ULDC) * Privacy Protection: Secure multi-party computation and differential privacy
They present case studies and examples to illustrate how deterministic extraction enhances the security and efficiency of these applications.
Advanced Techniques and Recent Developments
The monograph also covers advanced topics and recent developments in the field of deterministic extraction. These include:
* Reverse Deterministic Extraction: Recovering weak randomness from deterministic extractors * Composability and Amplification: Combining extractors to obtain stronger randomness * Information-Theoretic Security Analysis: Formalizing security guarantees based on information-theoretic principles
Accessibility and Readership
"Deterministic Extraction from Weak Random Sources: Theory and Applications" is written in an accessible and engaging style, catering to a wide audience. It is suitable for:
* Researchers in cryptography, information theory, and computer science * Graduate students seeking an in-depth understanding of deterministic extraction * Practitioners in cryptography and data security * Anyone interested in the fascinating world of randomness and its practical implications
"Deterministic Extraction from Weak Random Sources: Theory and Applications" is an invaluable resource for anyone seeking a comprehensive understanding of this essential technique. Its in-depth analysis, detailed explanations, and practical applications make it a must-read for researchers, students, and practitioners alike.
By mastering the principles and algorithms presented in this monograph, readers will gain the knowledge and tools to leverage the power of deterministic extraction in their own research and applications, unlocking the secrets of randomness in the face of adversity.
Long Descriptive Keywords for Alt Attribute
* Deterministic Extraction From Weak Random Sources Guide * Theory and Applications of Deterministic Extraction * Cryptography, Data Compression, and Privacy Enhancement * Leftover Hash Lemma, Wegman-Carter Algorithm, Universal Hashing * Recent Advances in Deterministic Extraction and Information-Theoretic Security Analysis
4.9 out of 5
| Language | : | English |
| File size | : | 9285 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 306 pages |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Steven M Friedson
Steven M Friedson Petros C Mavroidis
Petros C Mavroidis Mark Gillespie
Mark Gillespie Vikas Bansal
Vikas Bansal Ralph Manheim
Ralph Manheim Dan Slott
Dan Slott Paul F Grendler
Paul F Grendler Mohammed El Kurd
Mohammed El Kurd Lucy Score
Lucy Score Sophia K Apple
Sophia K Apple Terry Mcmillan
Terry Mcmillan Tanya Markul
Tanya Markul Ryan Watkins
Ryan Watkins Melissa Lowry
Melissa Lowry Seyla Benhabib
Seyla Benhabib Phillip Dutton
Phillip Dutton Penny Henderson
Penny Henderson Laura Vanarendonk Baugh
Laura Vanarendonk Baugh Rute Couto
Rute Couto Vincent Miles
Vincent Miles
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Dale MitchellDelve into the Profound Wisdom of Vedanta: An Introduction to Unveil the True...
Dale MitchellDelve into the Profound Wisdom of Vedanta: An Introduction to Unveil the True...
 Oliver FosterShining Light on the Mueller Report: Uncovering the Truth Behind the Russia...
Oliver FosterShining Light on the Mueller Report: Uncovering the Truth Behind the Russia... Nikolai GogolFollow ·12k
Nikolai GogolFollow ·12k Fernando BellFollow ·10.2k
Fernando BellFollow ·10.2k Jules VerneFollow ·9.2k
Jules VerneFollow ·9.2k Eddie BellFollow ·14.6k
Eddie BellFollow ·14.6k Tyler NelsonFollow ·8.7k
Tyler NelsonFollow ·8.7k Michael ChabonFollow ·14.3k
Michael ChabonFollow ·14.3k Carl WalkerFollow ·10.4k
Carl WalkerFollow ·10.4k Emilio CoxFollow ·19.7k
Emilio CoxFollow ·19.7k
 Jorge Luis Borges
Jorge Luis BorgesUnlock Your Inner Musician: The Ultimate Guide to...
Embark on a Musical...
 Carlos Drummond
Carlos DrummondQuick Reference Guide To Percussion Instruments And How...
Unleash your inner rhythm with...
 Roberto Bolaño
Roberto BolañoUnlock Your Guitar Potential: The Ultimate Guitar Mastery...
Are you ready...
 Fred Foster
Fred FosterLooking for Lady Dee: A Punk Rock Mystery
By [Author's Name] Looking for Lady Dee is...
 Jacques Bell
Jacques BellJourney into the Mystical Realm of "Heaven Polly Alice...
In the tapestry of literature, where...
 Julio Ramón Ribeyro
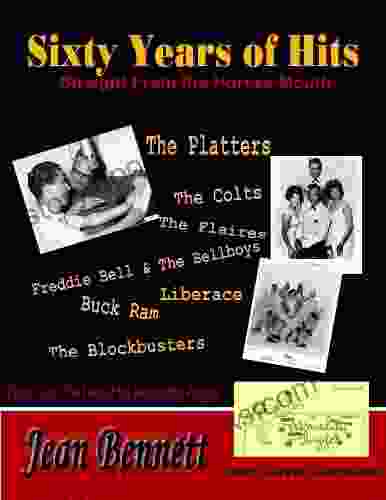
Julio Ramón RibeyroSixty Years of Hits: A Musical Journey Through Time
Music has the...
4.9 out of 5
| Language | : | English |
| File size | : | 9285 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 306 pages |